
Hello to the “Practical Linux for Pentesting & Bug Bounties” course! This course will particularly interest anyone with minimal IT experience who seeks to transition to Linux, penetration testing, and bug bounty. There is no prerequisite knowledge of Linux or programming; you don’t need it to navigate through old data. For basic operations, it is only necessary to have a computer, an internet connection, and a minimum of 4 GB RAM. It starts with learning to install Linux in your system, the basics of Linux, and writing the bash scripts for web-based attacks and Automation scripts.
In the course titled “Practical Linux for Pentesting & Bug Bounties,” you will learn and become familiar with numerous Linux commands, directory hierarchy, networking, and many other subjects. With Regedit, you can also configure software packages, system performance, user information, and network settings. The extremely applicable type adopts an environment identical to the active one, and therefore, you’ll be totally prepared once you enter the penetration testing or bug-hunting business. At the same time, you will develop your custom Bash script tools for such operations as Subdomain Enumeration, Directory Fuzzing, CORS Automation, and XSS Automation.
In addition, you will get additional sources with the personal Bash scripts to execute bugs and interview questions and answers to assist you in job interviews or internships. If at the end of the course “Practical Linux for Pentesting & Bug Bounties,” you are unfamiliar with Linux and do not know how to write Bash scripts, then you are in the right field: penetration testing and bug bounties.
Practical Linux for Pentesting & Bug Bounties Table of Contents:
- Introduction: 03:01
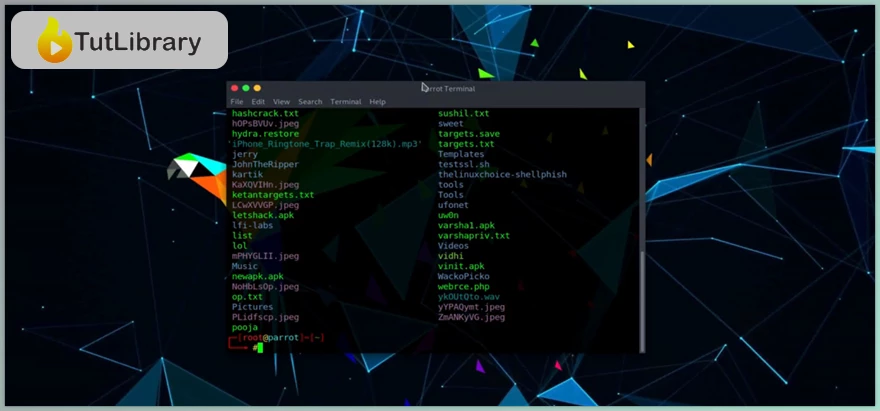
- Tour of Penetration Testing OS: 02:27
- Installation of VirtualBox: 04:54
- Installation of VMware: 03:48
- Installation of Linux ISO on VMware: 06:03
- Installation of Linux ISO on VirtualBox: 04:16
- Installation of Linux OVA on VMware: 03:33
- Installation of Linux OVA on VirtualBox: 02:28
- Windows Boot Process: 02:45
- Linux Boot Process: 09:39
- Breaking Root Password: 05:49
- Setting Password for GRUB: 08:07
- What are Package Managers: 04:54
- yum: 07:08
- brew: 04:26
- dpkg: 04:27
- rpm: 04:46
- chocolaty: 03:38
- apt: 02:52
- Searching for Package: 02:12
- Installing and Removing Package: 02:33
- Updating Package: 02:21
- Upgrading Package: 01:16
- Adding Repositories: 08:14
- GUI Package Manager - Synaptic: 03:58
- Installing with git: 02:52
- Linux System Information Commands: 05:35
- Linux Hardware Information Commands: 05:55
- Performance Monitoring Commands - Part 1: 03:27
- Performance Monitoring Commands - Part 2: 03:43
- User Info and Management Commands: 05:49
- File, Directory, and Deletion Commands: 11:23
- Directory Management Commands: 04:05
- Rename, Move, and Case Sensitive Commands: 04:18
- Symbolic Links Commands: 02:02
- File Reading Commands: 05:12
- Process and Kill Commands - Part 1: 03:21
- Process and Kill Commands - Part 2: 02:22
- Background and Foreground Commands: 02:25
- Fundamentals of Linux Permissions: 09:03
- Adding Permissions: 05:34
- Removing Permissions: 02:46
- Execution Permissions: 04:23
- Linux Octal Permissions: 02:52
- chown: 05:51
- chgroup: 02:28
- Linux Network Management - Part 1: 03:26
- Linux Network Management - Part 2: 02:06
- Linux Network Management - Part 3: 05:08
- Linux Network Management - Part 4: 03:37
- Linux Network Management - Part 5: 02:38
- Linux Network Management - Part 6: 05:00
- iwconfig: 05:41
- Spoofing your MAC Address: 04:07
- Linux Archive Management Commands: 04:55
- Linux Search and Pattern Commands: 05:24
- Linux SSH Management - Part 1: 06:39
- Linux SSH Management Live - Part 2: 02:56
- Linux SAMBA Management - Part 1: 08:17
- Linux SAMBA Management - Part 2: 04:53
- Linux File System Architecture: 01:39
- root - Part 1: 01:44
- root - Part 2: 02:11
- etc: 02:36
- home: 02:52
- Snapshot of Linux Booting Process: 00:28
- Quick and Faster Way of Assigning Permissions: 01:05
- Linux System Command: 01:43
- Linux System Information: 01:42
- Understanding Top Performance Monitoring Commands: 01:21
- Introduction to Linux Performance Commands: 01:26
- Understanding User Info Commands: 02:00
- Efficient Text Manipulation: Mastering Advanced Techniques in Linux: 04:09
Who is this course for?
- People who want to complete the course in Linux and hacking/penetration of web applications
- New users planning to use Linux for ethical hacking
- Automating bug bounty using only Bash Scripting for beginners who want to get started with it.
- Instructors who want to offer Linux for pen-testing
- Employees working in IT and cybersecurity, specifically in the penetration testing department
- Ethical hackers striving for knowledge of basic Linux
- Those applicants who are initially entering the cybersecurity field and searching for analyst jobs
- Employees in the corporate world responsible for managing SOC (Security Operations Center)
- Security experts who would like to patch up some of the flaws and design applications that are hard to crack.
Click on the links below to Download Practical Linux for Pentesting & Bug Bounties!
در حال پاسخ به :
















