
“Kali Linux Tutorial for Ethical Hacking & Penetration Test.” This is your undisputed entry pass to the world of ethical hacking, penetrating tests using Kali Linux we have prepared for those who have just started their journey into cybersecurity. Starting with the foundation, learning Linux distributions to the advanced level, and sieging powerful tools including but not limited to Wireshark, NMAP, Metasploit, and Burp Suite, you will be on a journey of learning a blend of theory with practical sessions.
Specifically, the course “Kali Linux Tutorial for Ethical Hacking & Penetration Test” provides an accessible means of understanding and using Kali Linux to those with perhaps basic computer literacy. You will explore the next basics of terminal and shell, Linux packages and repositories, and basic network reconnaissance. The approach used in the guide, along with the examples, ensures an understanding of the key principles and provides practical practice in running key hacker programs. In addition, our highly qualified tutors make a distinction in the quality of video and audio productions that make the learning process enjoyable throughout the course.
When the course is finished, you will be ready to manage operating system settings that control your Kali Linux and apply advanced security assessment applications effectively. you will have a conclusive understanding of the cybersecurity environment. So, if you want to be a white hat hacker, a lover of security threats, or are just fascinated with Kali Linux, the Kali Linux Tutorial for Ethical Hacking & Penetration Test is your ticket to riding the wave of one of the latest and most effective tools in the fight against network security threats.
Kali Linux Tutorial for Ethical Hacking & Penetration Test Table of Contents:
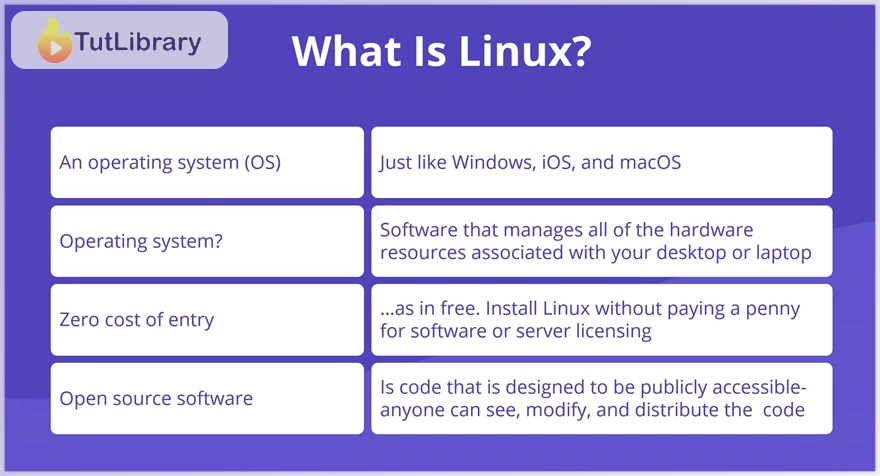
- Linux is believed to be more technical than the common OS, Windows and MacOS.
- Linux has unique versions that correspond to the user’s requirement level or expertise level.
- Linux is the operating system's fundamental layer, which is responsible for controlling the computer’s operations and managing hardware components.
- Based on the Debian distribution, Kali Linux is developed for detailed information security processes like penetration testing and forensics.
- Therefore, installing Kali Linux offers a starting point for security lovers and specialists.
- It is, therefore, important to teach a lesson on how to manage program updates/upgrades to enhance the system's security and performance.
- A general knowledge of the options for creating and deleting files and folders is also essential for proper organization.
- Since the management and administration of Linux systems are done through terminal commands, the more one masters the environment, the better the control over it will be.
- Socialization with hacking programs is an essential criterion for carrying out penetration testing and evaluation.
- That is why the components of Linux distributions, shell commands, and the Desktop environments are valuable additions to system understanding.
- Studying the Linux file structure and the graphical user interface improves operability and effectiveness.
- Laying out the various Kali Linux environments, such as through the use of virtual machines, makes security experiments achievable.
- Setting up real-life lab environments within VMware promotes towing the realistic feel and essence of the lab.
- Linux system administration begins with understanding elementary instructions and package management concepts.
- Tuning involves changing Kali Linux to enhance a particular function and/or security feature.
- Analyzing the monitoring tools is useful for evaluating the system performance and conducting security analysis.
- Thus, using network scanning, Metasploit basics, and password-cracking tools enhance security testing capacity.
Using information gathering and web application hacking tools increases proficiency in security assessment.
Who is this course for?
- Ethical hackers and penetration testers are working on strengthening the network and system security while developing weaknesses.
- The presented technologies will help cybersecurity specialists increase their abilities in the field of offense-security.
- Lovers of Kali Linux tools always look forward to the best time to use them to shake up network security and assess vulnerabilities.
- People interested in ethical hacking and penetration testing have diverse goals, and most of them are interested in broadening their knowledge.
- Students who pursue academics or certification with an intention to enter cyberspace or the IT industry are motivated.
Click on the links below to Download Kali Linux Tutorial for Ethical Hacking & Penetration Test!
در حال پاسخ به :















