
Our beginner-friendly course, "Ethical Hacking + Linux + SQL + Excel + Word : IT PRO v2”, is intended for newbies; it allows students to dive into a new area even if they have never touched computer networks. Introduction to Ethical Hacking, using Kali Linux as the primary tool in Penetration Testing and Security Auditing. Using tools and resources available in Kali Linux, you will investigate diverse aspects of information security and hacking, beginning with classifying hackers and coming up with techniques such as Windows security, account hacking, and password cracking.
Discover the specifics of threats like a virus, a worm, or a Trojan and get real-life tips on detecting or preventing it. Learn fundamental knowledge about encryption, such as ciphers, encoding tables, SQL Injection elementary concepts, website-building principles, website creation, and server-side scripts. This course, "EEthical Hacking + Linux + SQL + Excel + Word : IT PRO v2,” enhances your knowledge of such topics as Social Engineering, Phishing Attacks, and Reverse Engineering – and prepares you to learn the necessary tools and approaches to face contemporary threats in the area of cybersecurity.
Moreover, polishing skills in core instruments, including Microsoft Excel and Word, will make you perfectly competent in the diverse field of IT service.
Ethical Hacking + Linux + SQL + Excel + Word : IT PRO v2 Table of Contents:
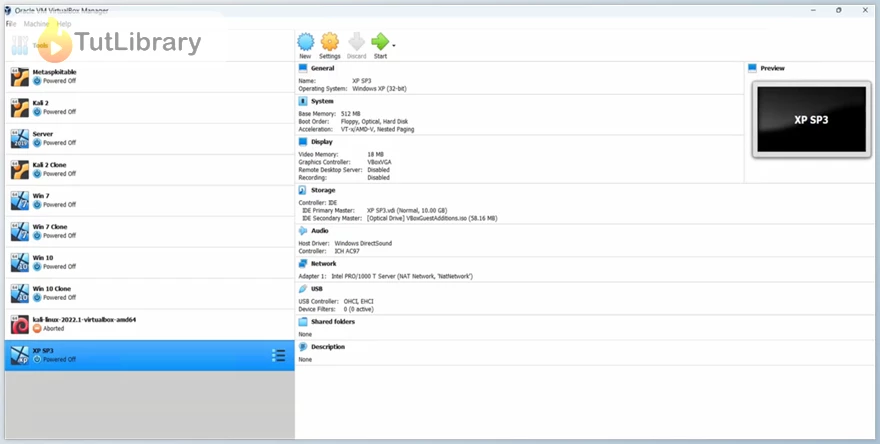
- Creating LAB-OS (11:33)
- OS 1 (09:47)
- OS 2 (07:29)
- OS 3 (I) (01:18)
- OS 3 (II) (07:28)
- Win 7 (07:27)
- Win 10 (05:49)
- Snapshots (02:44)
- Network ? (01:53)
- Network Configuration (06:02)
- Hacking (01:47)
- Hackers (07:34)
- Ping (03:20)
- Harvester (03:21)
- NSLOOKUP (02:36)
- Data Extraction (03:51)
- Mirroring (02:29)
- Nmap 1 (01:33)
- Nmap 2 (01:48)
- Nmap 3 (02:02)
- Nmap 4 (02:17)
- Nmap 5 (05:01)
- Zenmap (03:57)
- Finding OS (02:36)
- Topology Finding (03:19)
- Search Engine (07:21)
- Google Keywords (04:38)
- Steganography I (04:58)
- Steganography II (02:07)
- Steganography III (07:33)
- Steganography IV (01:58)
- Spoofing Email (09:10)
- ADS Spy (01:40)
- Keylogger (03:38)
- Intro (01:52)
- Interface (03:53)
- Database (09:01)
- DB Mode (03:59)
- DB Logical View (01:49)
- DB Objects 1 (02:31)
- DB Objects 2 (01:53)
- DB Objects 3 (02:17)
- DB Objects 4 (01:30)
- DB Objects 5 (06:38)
- Data Types 1 (03:02)
- Data Types 2 (01:44)
- Data Types 3 (02:34)
- Data Types 4 (02:16)
- Data Types 5 (01:42)
- Data Constraints 1 (03:04)
- Data Constraints 2 (03:42)
- Data Constraints 3 (01:54)
- Data Constraints 4 (01:40)
- Data Constraints 5 (01:08)
- Data Constraints 6 (02:42)
- SQL 1 (05:37)
- SQL 2 (07:25)
- SQL 3 (04:20)
- SQL 4 (02:19)
- SQL 5 (03:43)
- DDL 1 (00:52)
- DDL 2 (15:23)
- DDL 3 (02:17)
- DDL 4 (03:44)
- DDL 5 (04:25)
- DDL 6 (03:56)
- DDL 7 (00:38)
- DDL 8 (01:32)
- DDL 9 (06:35)
- DDL 10 (03:37)
- DDL 11 (04:23)
- DDL 12 (03:33)
- DML 1 (04:54)
- DML 2 (02:28)
- DML 3 (06:49)
- DML 4 (11:20)
- Functions 1 (00:48)
- Functions 2 (02:05)
- Functions 3 (06:53)
- Functions 4 (15:29)
- Numeric 1 (01:18)
- Numeric 2 (08:21)
- Numeric 3 (04:18)
- Date Time 1 (02:19)
- Date Time 2 (03:08)
- Conversion Func 1 (00:48)
- Conversion Func 2 (07:27)
- Conversion Func 3 (08:01)
- Joins 1 (02:47)
- Joins 2 (08:07)
- Congratulations (00:04)
Who is this course for?
- Anyone who is interested in Cyber Security
Click on the links below to Download Ethical Hacking + Linux + SQL + Excel + Word : IT PRO v2!
در حال پاسخ به :















