
Discover the field of mobile penetration testing in our Android Hacking and Penetration Testing course titled “Mobile Penetration Testing of Android Applications.” Intended for beginners and advanced users, this tutorial is a video course where you will learn how to apply and analyze the security of Android mobile applications. With the usage of the Android operating system, which stands at over 80% of all Active mobile devices globally, its security is of utmost importance, and it is important to comprehend how one can minimize threats.
Dive into the Android application hacking as you transition all the web hacking techniques to the mobile platform. Learn about OWASP Top Ten Mobile and Web with chances to find out about often-used security flaws and features. This is an intermediate course titled “Mobile Penetration Testing of Android Applications” that will allow you to improve your knowledge in the sphere of cybersecurity and prepare for the threats in the Android environment.
Mobile Penetration Testing of Android Applications Table of Contents:
- Android Studio (11:21)
- AVD Manager is missing? ADB Connection and Monitor in Android Studio 3.5/newer (01:27)
- Android Debug Bridge (ADB) (06:23)
- Android emulator or Android Device? (06:57)
- Android rooting (05:43)
- Setting up a Proxy for Android (10:25)
- Installing CA Certificate (05:41)
- Virtual Machine Download (00:07)
- Android Vulnerable Application Setup (03:43)
- APK file Structure. AndroidManifest XML file (07:01)
- Reversing to get the Source code of the Application - decompiling with dex2jar (10:53)
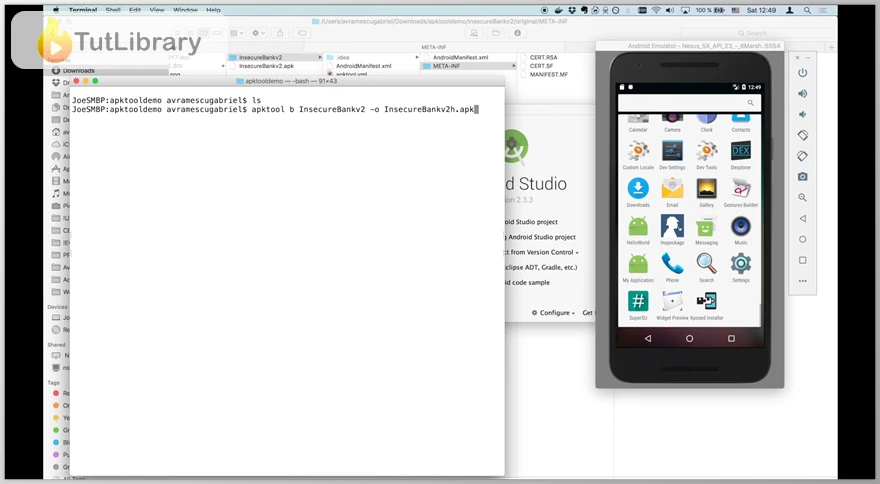
- Reversing and Re-compiling with APKTool (10:55)
- APK Teardown in a Nutshell using Dexplorer on your Android Device (02:56)
- Static vs Dynamic Analysis (05:58)
- Static Analysis of Android Application using QARK (13:05)
- Dynamic Analysis of Android Application using Inspeckage and Xposed (15:36)
- MobSF - Mobile-Security-Framework. Malware analysis (10:48)
- Automated Security Assessments with Drozer (08:45)
- Intercept traffic using Wireshark and tcpdump (05:22)
- Intent Sniffing (05:23)
- Fuzzing using Burp - Password Brute-Force. Username enumeration (11:58)
- General Description (04:10)
- Automatic bypass of certificate pinning (08:51)
- Manual bypass of certificate pinning (31:50)
- Bonus - Take control over an Android phone using metasploit (06:35)
- Penetration Testing Cheat Sheet (18:59)
- OWASP Top 10 Mobile Vulnerabilities and Attacks (13:22)
- Further research - Automatic and Manual Scanning for Vulnerabilities (18:15)
- For Developers - Android Security Guidelines (01:21)
- Bonus - Easily download any APK file from Google Play directly on your PC (01:08)
- Final Words (00:15)
- Further information (00:16)
- Core Problems - Why Web Security (07:33)
- Spider and Analyze a Website using Burp (05:26)
- Brute-forcing Web Resources using Dirb and Dirbuster (10:38)
- SQL injection (09:09)
- Exploiting SQLi using Sqlmap and Getting Remote Shell (10:07)
- Upload and Remote File Execution (10:43)
- Alternative setup - Download Burp. Free vs Paid (01:25)
- Proxy - General Concept (04:24)
- Target Module (10:21)
- Proxy Module - part 1 (11:48)
- Proxy Module - part 2 (10:06)
Who is this course for?
- Penetration testers, security professionals, and amateurs
- Web and mobile application developers
- Security enthusiasts
Click on the links below to Download Mobile Penetration Testing of Android Applications!
در حال پاسخ به :











