
Welcome to "Ethical Hacking: Build Ransomware with Control Center POC," a hands-on course designed to teach you how to ethically create and manage advanced ransomware. This course is perfect for anyone interested in cybersecurity, whether you're a beginner or an IT professional. You'll need basic computer skills, a stable internet connection, and a willingness to learn. We'll guide you through setting up your development environment with Python, PHP, and the necessary tools.
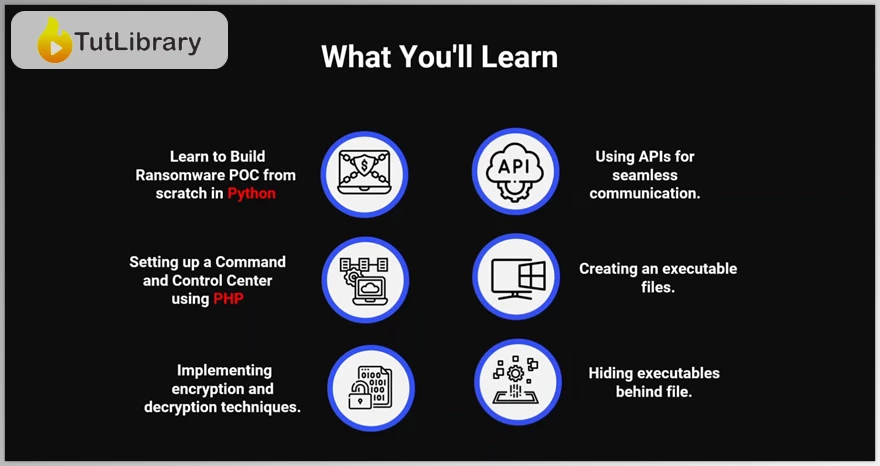
In this course, you'll learn step-by-step how to build a fully functional ransomware application using Python. You'll understand the essentials of encryption and decryption and how to create a command and control center using PHP. Additionally, we'll cover how to integrate APIs for communication between your ransomware and its control center, package your application into an executable file, and use advanced techniques like steganography to hide your executable within an image.
By the end of this course, "Ethical Hacking: Build Ransomware with Control Center POC," you'll have practical, hands-on experience in creating and managing ransomware ethically. This will not only expand your knowledge but also improve your skills in cybersecurity. Join us in exploring this fascinating field and gain valuable insights into the workings of ransomware and control systems.
Ethical Hacking: Build Ransomware with Control Center POC Table of Contents:
- Introduction - 01:23
- Project Overview - 11:53
- Demo of the Complete Ransomware - 16:32
- Simple Encryption Concept Implementation - 12:46
- Simple Decryption Concept Implementation - 10:30
- Main GUI Layout - 25:28
- Initialization & Setup - 17:17
- Encryption Tool Class - 04:57
- File Encryption Functions - 12:46
- User Manual Creation & Key Management - 16:16
- Dialog Classes for User Interactions - 26:38
- DecryptorApp Class & Initialization - 24:19
- DecryptorApp Methods - 19:43
- Decryption Process - 16:42
- Timer & Cleanup Methods - 41:24
- Main Execution - 16:42
- Initial Configuration and Setting up XAMPP - 13:36
- Includes Base Configuration Files - 42:19
- Developing Register Page - 30:57
- Developing Login & Logout Page - 24:44
- Developing Dashboard for Command & Control - 01:00:57
- Developing Profile Page - 41:13
- Creating and Implementing APIs for Kill Signals and Encryption Keys - 21:07
- Adding Remote Sendkeys and Receiving Kill Signals - 08:37
- Packaging the Application into an Executable - 11:30
- Hiding the Executable Behind an Image - 12:50
Who is this course for?
- Aspiring Ethical Hackers: If you want to start a career in ethical hacking and cybersecurity, this course is perfect for you.
- Cybersecurity Enthusiasts: Curious about how ransomware works and how to protect against it? This course will satisfy your curiosity and expand your knowledge.
- Developers and IT Professionals: Looking to broaden your expertise in cybersecurity, including ransomware creation and command control centers? This course is a great fit.
- Students and Learners: Studying computer science or cybersecurity? Gain practical, hands-on experience that complements your studies.
- Intermediate Programmers: Have some programming experience and want to apply your skills to exciting cybersecurity projects? This course will help you do just that.
Click on the links below to Download Ethical Hacking: Build Ransomware with Control Center POC!
در حال پاسخ به :















