
Introduction to the world of threat hunting with data science guidance and a free trial on Splunk is as easy as ABC with this course. This course helps you establish a basic knowledge of network security, Splunk, and SPL, providing you with the basics of threat detection. This way, you will learn how Splunk is an essential center for data consumption, processing, and even real-time visualization, focusing on security issues and their immediate response.
Dive into the implementation of data science on Splunk, where you’ll see how statistical analysis, machine learning, and even natural language processing can boost the effectiveness of security operations’ threat detection. Real-life examples shed light on how these techniques enable the cyber defenders to detect out-of-ordinary usage patterns by users and various abovementioned subtle network activities, as well as expose covert malware threats. Familiarizing yourself with Splunk’s Machine Learning Toolkit (MLTK) will also enable you to develop a unique machine-learning model for actuating threatened predictions.
At the end of the course, you will appreciate how data science and Splunk complement each other in strengthening cybersecurity stances. Whether one finds oneself at the starting line, in the middle, or is even an expert, all newcomers to the field can benefit from “Threat Hunting with Data Science and Splunk for Beginners,” which promotes a notable advancement in the protection of assets from threats in the digital frontier.
Threat Hunting with Data Science and Splunk for Beginners Table of Contents:
- Introduction (02:07)
- Splunk Installation (03:28)
- Splunk Bulk Apps and Addons Installation (01:58)
- Splunk Boss of The SOC (BOTS) Installation (03:25)
- Import Lab Attacks Data to Splunk (02:49)
- Data Science and Splunk (01:07)
- Standard Deviation (03:39)
- Normal Distribution or Gaussian Distribution (04:24)
- Empirical or 68–95–99.7 rule (03:55)
- Standard Normal Distribution (Z-Score) (06:16)
- User Access Anomalies Hunting (02:52)
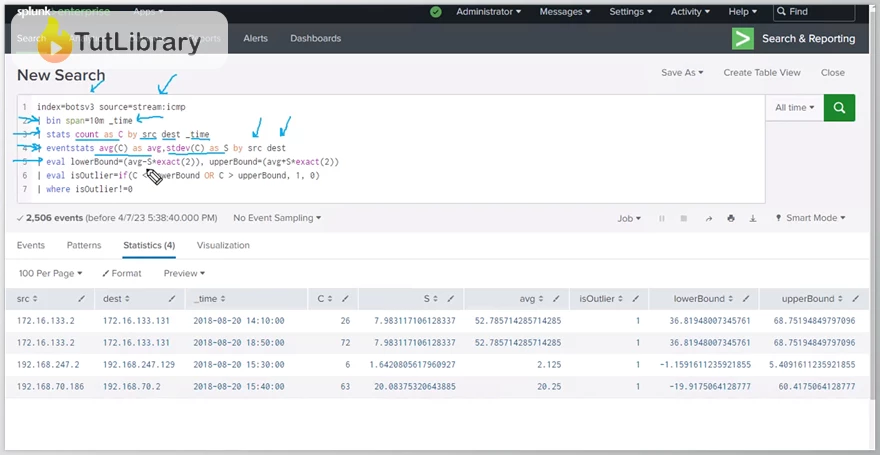
- SMB Traffic Anomaly Detection (03:30)
- Windows Process CommandLine Outlier Detection (01:51)
- Detecting Log Disruption Attacks (02:37)
- Network Traffic Volume Outliers Detection (02:07)
- Malware Activity Detection by Math (02:56)
- Let Splunk Detect Attacks for You (04:27)
- Malware Detection with Shannon Entropy (04:03)
- What is Splunk Machine Learning Toolkit (01:07)
- Splunk MLTK App Installation (01:52)
- DNS Outlier Detection with MLTK (02:42)
- Increase Fault Tolerance for Data Science with Splunk (04:05)
- What is Domain Generation Algorithm (DGA)? (03:04)
- Splunk DGA App Installation (04:02)
- DGA Detection with Splunk (01:42)
- NLP Text Analytics using Splunk (07:15)
Who is this course for?
- SOC Analysts in Security Operations Centers
- Cyber Threat Hunters
- Engineers specialized in Splunk
- Security experts and analysts that operate in threat intelligence.
- The Digital Forensics and Incident Response (DFIR) Professionals
Click on the links below to Download Threat Hunting with Data Science and Splunk for Beginners!
در حال پاسخ به :
















