
‘Microsoft Copilot for Security’ course is here! Whether you are a beginner in IT or want to enhance your expertise, this training is ideal. This journey of using generative AI to prevent and mitigate cybersecurity threats will be easy and enjoyable.
Initially, we shall be introduced to the basics, which include understanding what a Security Operations Center (SOC) does and how one can detect cyber threats. Furthermore, there will be a discussion on Microsoft Defender and Azure services, as they are important in the preservation of digital assets.
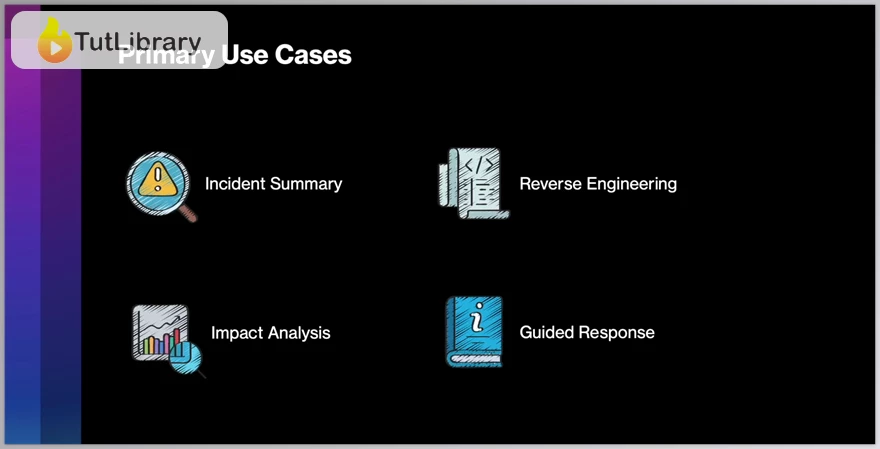
Then comes an introduction to Microsoft Copilot itself, displaying how it works with other tools installed within it to become threat detector software. Also discussed is its integration with other Microsoft security tools, such as Defender XDR and Sentinel, respectively, as well as third-party plug-ins for additional protection.
At the end of ‘Microsoft Copilot for Security,’ you will possess ample knowledge of MS Copilot, raising your organizational defense against ever-evolving risks.
Join us and download this course for FREE NOW!!
Microsoft Copilot for Security Table of Contents:
- Welcome (00:52)
- Course Slides (00:02)
- IMPORTANT - Basics (00:17)
- IMPORTANT - Demos (00:16)
- FAQs (00:15)
- Complexity and Cyber Security Challenges (09:24)
- What is a SOC? (03:53)
- SOC Tier Model (03:11)
- Cyber Security Incident Response Process (02:59)
- EDR, XDR, SIEM & SOAR (04:50)
- Blue, Red & Purple Teaming (04:32)
- What is a Threat? (01:34)
- Intelligence, Threat Intelligence & Cyber Threat Intelligence (CTI) (02:46)
- What is CTI? (02:07)
- Threat, Vulnerability & Risk (01:46)
- Threat-Informed Defense (03:15)
- Tactics, Techniques & Procedures (TTPs) (03:00)
- IOCs & IOAs (02:34)
- Pyramid of Pain (03:11)
- CTI Sources (01:53)
- What is a Vulnerability? (02:02)
- Common Vulnerabilities and Exposures (CVE) (02:37)
- Common Vulnerability Scoring System (CVSS) (05:05)
- Cloud Computing Properties (03:00)
- Cloud Computing Types (02:12)
- Azure Global Backbone (01:54)
- Shared Responsibility Model (04:30)
- Azure Resource Hierarchy (03:13)
- Azure Subscription Types (02:03)
- Entra ID Tenants and Azure Subscriptions (01:39)
- Zero Trust (03:40)
- The Microsoft Security Cosmos (04:35)
- Defending Across Attack Chains (03:09)
- What is a Large Language Model (LLM)? (02:39)
- What is a Prompt? (03:41)
- AI Models (01:20)
- LLM Architecture (03:27)
- OWASP (01:13)
- OWASP Top 10 for LLMs (05:48)
- How Adversaries Leverage AI (03:33)
- Microsoft Responsible AI (02:56)
- Shared Responsibility in AI (04:02)
- What is Copilot for Security? (05:22)
- From Prompt to Response (02:05)
- Architecture (05:41)
- Extending Copilot with Plugins & more (03:41)
- Privacy Implications (02:11)
- Authentication & RBAC (06:09)
- Standalone vs. Embedded Experience (01:21)
- Pricing (02:23)
- IMPORTANT - DO NOT SKIP (00:28)
- Onboarding Requirements (01:29)
- Demo: create compute capacities (03:45)
- Demo: Setup Copilot for Security (14:58)
- Creating Effective Prompts (12:04)
- Demo: Prompt Usage Monitoring (00:46)
- Demo: Incident Investigation Promptbook (14:36)
- Demo: Suspicious Script Analysis Promptbook (17:30)
- Demo: Threat Actor Profile Promptbook (17:15)
- Demo: Vulnerability Impact Assessment Promptbook (09:38)
- Demo: CTI Prompts (21:49)
- Demo: Vulnerability Assessment Prompts (09:38)
- Demo: Setup Sentinel (04:46)
- Demo: Sentinel Incident Investigation (05:30)
- Demo: Entra ID Prompts (09:24)
- CIRCL Hash Lookup (03:59)
- Demo: Shodan.io (07:59)
- Demo: Shodan.io Plugin (04:41)
- Demo: UrlScan (05:12)
- Custom Promptbooks (03:57)
- Custom Plugins (03:48)
- Important Resources (03:58)
- Bonus (00:58)
Who is this course for?
- SOC Analyst
- Security Architect
- Security Manager
- Security Professional
- Security Engineer
- Security Consultant
- CISO
- Cyber Threat Hunter
Click on the links below to Download Microsoft Copilot for Security!
در حال پاسخ به :











