
One can hardly talk about modern technologies without referring to algorithms. They are just action plans commonly used to accomplish tasks while incorporating value inputs into the procedures. The book Algorithms: Big Data, Optimization Techniques, Cyber Security Promising Algorithms organizes the best algorithms in various specific areas, including Big Data, Artificial Intelligence, Optimization Techniques, and Cloud and Cyber Security Systems. It will further investigate the strengths of such algorithms and the weaknesses of some of them.
Algorithms: Big Data, Optimization Techniques, Cyber Security Table of Contents:
- Rajiv Ranjan Giri, Richa Indu, Sushil Chandra Dimri: Machine learning-enabled techniques for speech categorization
- Akash Dogra, Shiv Ashish Dhondiyal, Sushil Chandra Dimri: Comprehensive study of cybersecurity issues and challenges
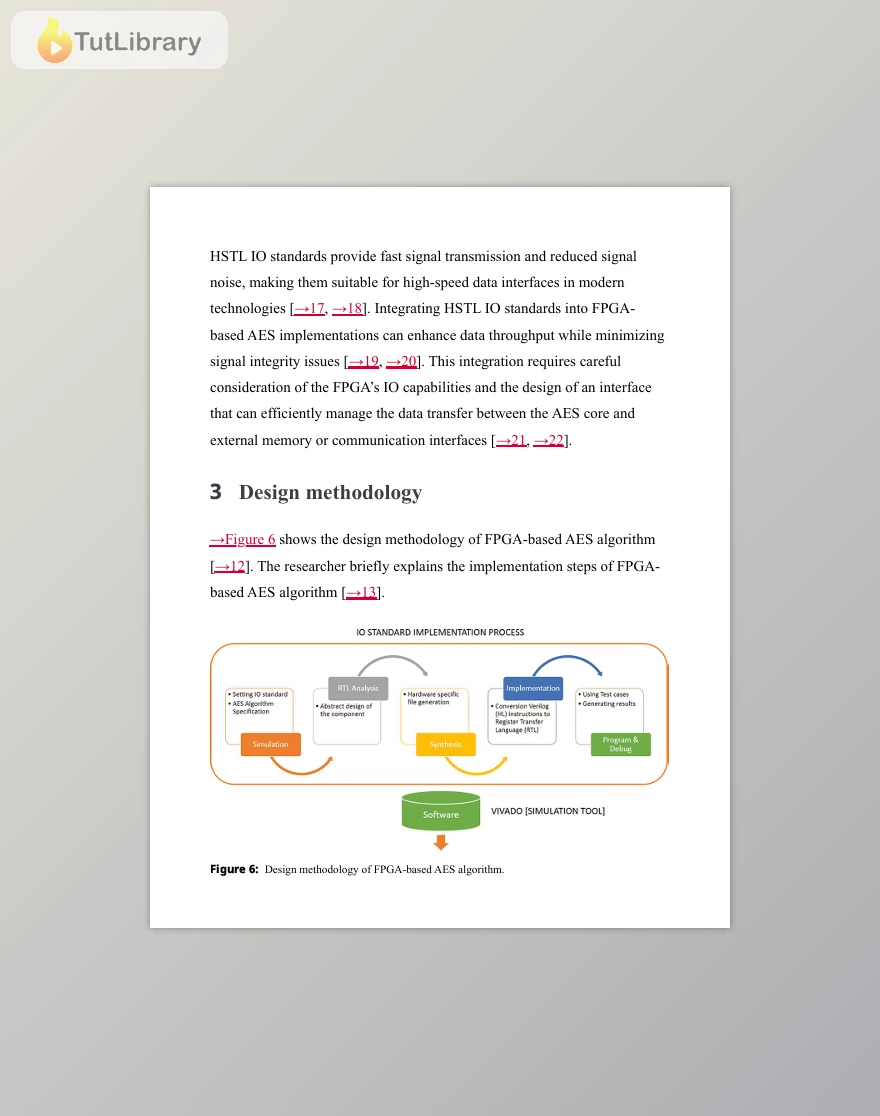
- Chandrashekhar Patel, Bhanu Priya Yadav, Aditi Saxena: An energy-efficient PGA-based implementation of AES algorithm using HSTL 10 standards for new digital age technologies
- Bhawnesh Kumar, Ashwani Kumar, Harendra Singh Negi, Ishwari Singh Rajput: A comparative study on security issues and clustering of wireless sensor networks
- Deonarain Brijlall, Tauqeer Ahmed Usmani, Richa Indu: Heuristic approach and its application to solve NP-complete traveling salesman problem
- Megha Shah, Akshay Kumar, Shristi Kharola, Mangey Ram: Assessment of fake news detection from machine learning and deep learning techniques
- Harendra Singh Negi, Aditya Bhatt, Vandana Rawat: Spam mail detection using various machine learning methods and their comparisons
- Rahul Bijalwan, Vandana Rawat, Akshita Patwal, Sudhanshu Maurya: Cybersecurity threats in the modern digital world
- Parth Gautam, Apurva Omer, Jeetendra Pande, Devesh Bora: Mechanism to protect the physical boundary of organizations where private and public networks encounter
- Bhawnesh Kumar, Aditya Bhatt, Neeraj Panwar: Combining binary search and insertion sort for a sorting method suitable for small input sizes
Who is this course for?
- Tech enthusiasts
- Students
- Professionals in technology fields
- This paper will target the following audiences whose insights are crucial to this research: Big Data enthusiasts, AI enthusiasts, optimization technique users, and cyber security experts.
- Every individual seeking to know more about the efficiency and ineffectiveness of high-performing algorithms.
Click on the links below to Download Algorithms: Big Data, Optimization Techniques, Cyber Security!
در حال پاسخ به :













