
In the advanced “x64 Assembly Language and Reverse Engineering Practicals” lectures, you will learn assembly language and reverse engineering. The cool tool we will use is x64dbg, which, to some extent, allows you to look inside any program and mess with it as you please, similar to a car mechanic.
This topic is easily defined by its name, “x64 Assembly Language and Reverse Engineering Practicals” – it is primarily practical. Aside from lectures and PowerPoint presentations, this is the kind of stuff that is real in practice. Finally, you will analyze working systems, for whom they work, how they work and, maybe, make them work in a way it has not worked before. From the identification of weaknesses to the inclusion of your code into the already existing system, this is going to be like solving technological crimes.
By the end of this article, you will have learned some SERIOUS skills. You’ll be an expert in x64 assembly, your best buddy with x64dbg, and you will have a feeling for mastering any software in any given situation. No matter whether you design your wasp-like cybersecurity programs, develop the most enchanting software, or love to dissect technologies like a sci-fi aficionado, this course named- x64 Assembly Language and Reverse Engineering Practicals will turn you into the ninja of your sphere in no time.
x64 Assembly Language and Reverse Engineering Practicals Table of Contents:
- Introduction - 06:40
- Installing Virtual Machine and x64dbg - 03:50
- Why Use a Debugger for Learning Assembly Language - 05:10
- x64 Instructions - 06:00
- Write Your First Instruction - 07:13
- Storing Number Constants in Memory - 13:36
- Storing String Constants in Memory - 07:03
- Creating Variables - 04:59
- How to Zero Out a Register Using XOR - 02:26
- ADD Instructions - 04:02
- Creating a New Template - 01:44
- Partial MOV Instructions - 03:13
- Basics of PUSH and POP - 06:16
- Exercise on PUSH and POP - 02:37
- Intro to MOV Instructions - 00:50
- Practical on MOV Instructions - 03:43
- XCHG Instruction - 03:57
- XCHG Memory - 06:30
- INC and DEC - 04:18
- NEG - 03:16
- ADD and SUB - 07:26
- Intro to the Register Flags - 02:45
- CF Flag - 03:15
- OF Flag - 04:42
- SF Flag - 02:07
- ZF Flag - 01:43
- Introduction to Bitwise Logical Operations - 03:40
- AND Operations - 05:40
- OR Operations - 07:08
- XOR Operations - 05:09
- Flags Register - 04:58
- NOT Operation - 01:51
- Introduction to Jumps - 01:19
- JMP Instructions - 11:13
- TEST Instructions - 08:13
- CMP Instructions - 03:36
- Conditional Jumps - 11:46
- Signed Conditional Jumps - 08:27
- Implementing If Statements - 07:36
- Implementing If-Else Statements - 09:26
- Multiple IF Tests - 09:05
- WHILE Loops - 09:30
- DO-WHILE Loops - 07:55
- Introduction to Arrays in x64dbg - 06:09
- Looping Through an Array - 08:18
- LEA Instructions - 09:08
- MUL Instructions - 05:37
- DIV Instructions - 04:48
- IMUL Instructions - 07:30
- The Stack - 12:40
- Creating Stackframes, CALL and RET Instructions - 05:35
- Calling Conventions - 07:24
- Simple Function Call with 4 Args and No Local Variables - 07:27
- Function Call with 4 Args and 4 Local Variables - 10:36
- Function Call with 5 Args - 07:45
- Function Call with 6 Args - 10:29
- Function Call with 7 Args - 13:53
- Introduction to the Practicals - 03:35
- How to Check Exe Type - 08:02
- Phishing for Passwords - 03:34
- How to Reverse a Jump and Patch the File - 04:25
- The Comment Tracing Method - 17:36
- How to Directly Access Memory to Modify Password and Patch the Exe File - 06:21
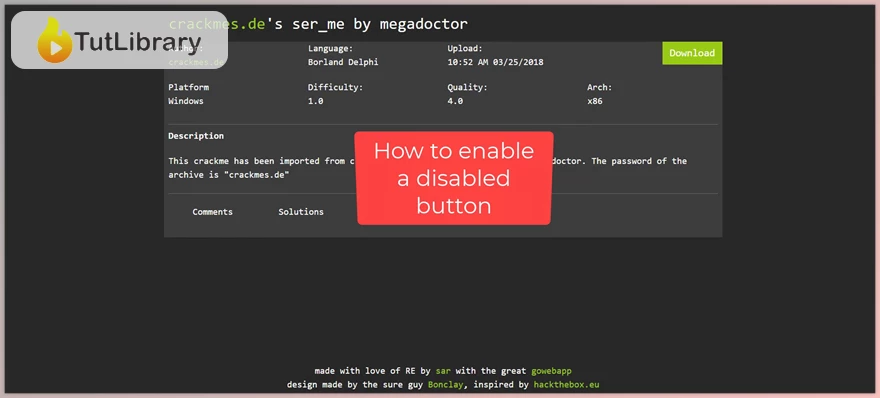
- Enabling a Disabled Greyed Out Button - 06:04
- How to Remove a Nag Message Box - 05:16
- Patching to Accept Any Serial Key and Also to Modify the Message Box - 08:46
- Tracing Username - 26:09
- Tracing Password - 07:44
- Tracing EAX Values - 11:22
- Patching to Show the Right Message - 04:02
- Tracing EAX Values to Get Password - 12:34
- Patching to Show Congrats Message - 05:17
- Loop Tracing Part 1 - 15:16
- Loop Tracing Part 2 - 12:39
- Loop Tracing Part 3 - 08:59
- Identifying Multiple Patching Options to Always Show the Good Message - 03:27
- Loop Tracing Registration Number - Part 1 - 10:55
- Loop Tracing Registration Number - Part 2 - 05:58
- Proper Way to Patch MessageBox - 08:54
- Comment Tracking Technique - Part 1 - 10:45
- Comment Tracking Technique - Part 2 - 06:41
- Patching to Show the Good Message - 03:23
- Creating a Self-Keygen - 10:01
- Modifying MessageBox Caption Using CodeCaves - 08:19
- Phishing for the Serial - 11:50
- Improvise an Alternative MessageBox to Show Serial Key - 11:45
- Fast Tracing by Toggling the ZF Flag - 09:21
- Patching Multiple Jumps with Block NOPs - 03:39
- Installing Process Hacker - 02:34
- Behaviour Analysis - 07:00
- Defeating Anti-Debugger and Killing the 1st Nag - 06:31
- Killing the 2nd Nag and Avoiding Patching Relocation Memory - 03:57
- Killing 3rd Nag and Using Intermodular Exit API to Quit - 05:08
- Tracing the Algorithm for Key Generation - 12:07
- Inject Own printf Function from Within an Exe to Print Out Serial Key - 12:24
- Behaviour Analysis - 04:16
- Tracing Length of Secret Code - 10:24
- Analysing x64 Fastcall Parameters - 07:23
- Behaviour Analysis - 19:00
- Bypassing Encryption by Analysing CMP Instructions - 15:43
- Bypassing Encryption by Patching - 03:53
- Debug a UPX Packed Binary - 09:53
- Phish for Password Without Using String Search - 13:36
- Patch Memory with Python - 11:45
- Call Stack Method and Identifying AOB (Array of Bytes) for Memory Scan - 09:32
- Load and Patch Memory with Python - 05:14
- Where to Go for More Courses on Reverse Engineering - 02:39
Who is this course for?
- The kind of graduates that would complete the course “Assembly Language Programming for Reverse Engineering.”
- Thus, this paper is for those who are well-conversed with x86 Assembly (32-bit) to enhance their knowledge of x64 (64-bit) Assembly.
- The objectives of reading the book to the security researchers who wish to improve reverse engineering knowledge.
Click on the links below to Download x64 Assembly Language and Reverse Engineering Practicals!
در حال پاسخ به :















