
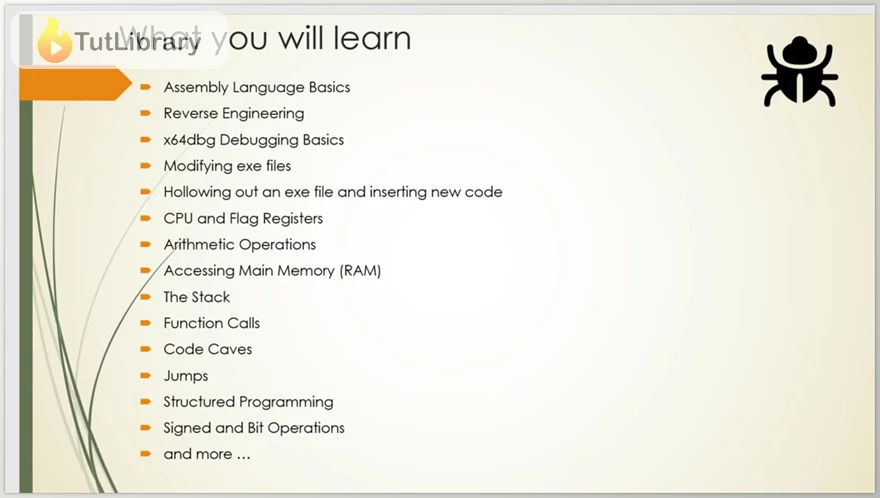
Discover the tricks of program manipulation and study AS Instruction Set for Reverse Engineering using the most selected course, “Assembly Language Programming for Reverse Engineering.” Suitable for novices and intermediate users of C language, you will be taken through the basics of the assembly language and the abilities required to analyze and change executable files to one’s benefit.
Contrary to most tutorials that include isolated assemblers, such as NASM or FASM, Assembly Language Programming for Reverse Engineering is a unique attempt that submerges you directly into the x64dbg debugger. You will learn assemblies starting from basic concepts, and using numerous practical examples, you will tie the knowledge into a coherent whole.
You will learn advanced practical concepts, including Memory segment Manipulation, Code cave exploitation, & Function creation, from adding small modifications to the existing code to adding new functionality. This combination of assembly language and reverse engineering knowledge is rather scarce, which makes this blog a valuable source of information for young security researchers, Malware analysts, and people interested in computer software security.
Assembly Language Programming for Reverse Engineering Table of Contents:
- Installing the Tools - 05:43
- Binary and Hexadecimal Number Systems - 09:50
- Introduction to xdbg Debugger - 17:47
- Debugger Stepping Basics - 04:52
- How to Hollow Out an EXE File - 11:03
- Introduction to CPU Registers - 09:43
- The MOV Instruction - 12:50
- Addition Using Full Registers - 11:40
- Addition of Partial Registers - 11:59
- Subtraction - 08:28
- INC and DEC Instructions - 11:06
- MUL Instructions - 14:37
- DIV Instructions - 15:10
- DIV Exercises - 14:48
- Register to Memory and Memory to Register - 13:35
- MOV to Memory and Direct Memory Patching Techniques - 04:51
- Memory Exercise - 11:43
- Pushing Register Values to the Stack - 13:45
- Popping Stack Values to Registers - 10:53
- How to Push Constants and Strings to the Stack - 06:20
- Introduction to Function Calls - 09:03
- Function Call with 2 Parameters - 11:20
- Exercise: Function Calls with 2 Parameters - 11:38
- Exercise: Function Calls with 3 Parameters - 08:41
- Intro to Input Output in Assembly - 12:16
- How to Read in Numbers and Output It Again - 08:17
- How to Read in Strings and Output It Back to User - 09:27
- Introduction to Code Caves - 14:20
- A Simple Code Cave - 06:43
- Code Cave Hello - 11:08
- Exercise: Get Firstname, Lastname - 25:12
- Project Description - 01:07
- Designing the Solution - 07:25
- Coding the Calculator - 24:01
- Introduction to Functions That Return a Value - 06:20
- Exercise on strlen() Function - 18:04
- Intro to the Flags Register and the ZF Flag - 06:16
- The SF Flag - 06:39
- The CF Flag - 07:00
- The OF Flag - 05:47
- Which Flag to Look: OF or CF? - 02:04
- Introduction to Jumps and JZ - 07:33
- JNZ Jump - 03:37
- JZ Loops - 06:07
- JNZ Loops - 04:12
- Other Conditional Jumps - 01:42
- Introduction to Compare Instructions - 05:52
- Practical on the CMP Instructions - 06:36
- Comparing Unsigned and Signed Numbers - 07:18
- Introduction to Structured Programming and If-Else Statements - 10:44
- For Loops - 08:22
- While Loops - 07:35
- Break out of Loops - 07:51
- Graph View, Trace Animate, and Principles of Jumps - 09:49
- NEG Instruction - 03:14
- Signed and Unsigned Extensions - 05:53
- Practical on Signed and Unsigned Extensions - 08:54
- Converting Bytes and Words Using CBW and CWDE - 05:44
- Converting Bytes and Words Using CWD and CDQ - 04:58
- IMUL and IDIV - 07:40
- Example of IDIV - 05:40
- Introduction to Boolean Algebra - 06:14
- Bitwise Instructions - 13:32
- Arithmetic Shifting - 07:01
- Rotate Instructions - 04:16
- Exercise on Bitwise Operations - 13:52
- Introduction to Memory Arrays - 11:43
- A Practical on Memory Arrays - 08:30
- Introduction to the LEA Instruction - 11:21
- A Simple LEA Implementation - 15:10
- LEA with Counter - 08:57
- LEA with Loop - 09:31
- Intro to Data Structures - 05:24
- Hands-on Practical on Data Structs - 06:53
- Introduction to String Instructions - 09:24
- The Direction Flag (DF Flag) - 08:05
- LODS Instructions - 09:45
- Exercise: LODS Adder - 06:37
- The MOVS Instructions - 10:06
- The REP Instruction - 03:34
- The SCAS Instructions - 07:39
- The CMPS Instructions - 05:45
- Introduction to CALL and RET - 09:59
- The Importance of Saving Register States - 08:13
- Nested Function Calls - 07:50
- Calling Conventions: Using Registers to Pass Params to Functions - 05:49
- Passing Parameters via the Heap (Global Data) - 04:19
- Passing Parameters via the Stack - 10:45
- Cleaning the Stack - 08:19
- Stack Frames - 07:46
- Stack Frame Practical - 13:29
- Introduction to the Call Stack - 13:04
- Practical on Traversing the Call Stack - 12:30
- Introduction to WinAPI - 08:41
- ReadFile and WriteFile - Theory - 09:26
- ReadFile and WriteFile - Practicals - 10:51
- Theory on the CreateFile Win32 API - 05:52
- Practical on the CreateFile Win32 API - 11:47
- Understanding External Functions - 03:44
- Practical on External Functions - 05:06
- Bonus Lecture - 02:39
- UPDATE: Continue Your Journey with x64 (64-bit) Assembly - 00:14
Who is this course for?
- Security researchers and students
- Reverse Engineers
- Any person who desires to learn Assembly Language for the purpose of being a software hacker or technically a hacker.
Click on the links below to Download Assembly Language Programming for Reverse Engineering!
You are replying to :








![Rust for Programmers - Coming from another language [2024] - Learn the Most Important Features of Rust](https://tutlibrary.com/filemanagercontent/files/1/searchsmall/425-banner.png)







