
Be ready for the CISSP exam with the help of our course “CISSP, 4th Edition - Sari Greene”. They provide you with over 32 hours of video instruction to cover general knowledge and skills with reference to the examination.
Depending on the specific exam area that is covered, each lesson presents the exam topics in a simple and clear manner. It is also full of lively quizzes and challenges to encourage learning as you go along the course. Also, by analyzing real-life examples, you learn to implement everything explained into your practice.
If you are new to the world of information security or if you already have some cybersecurity knowledge, this course, “CISSP, 4th Edition - Sari Greene,” will be rather valuable for you. Although previous experience in a few associated fields would be an advantage, anybody will find this course insightful and useful.
Join us NOW in this exclusive course and start getting ready for your CISSP exam!
CISSP, 4th Edition - Sari Greene Table of Contents:
- Introduction
- CISSP: Introduction
- Module 1: Domain 1 Security and Risk Management
- Module Introduction
- Lesson 1: Understand, Adhere to, and Promote Professional Ethics
- Learning objectives
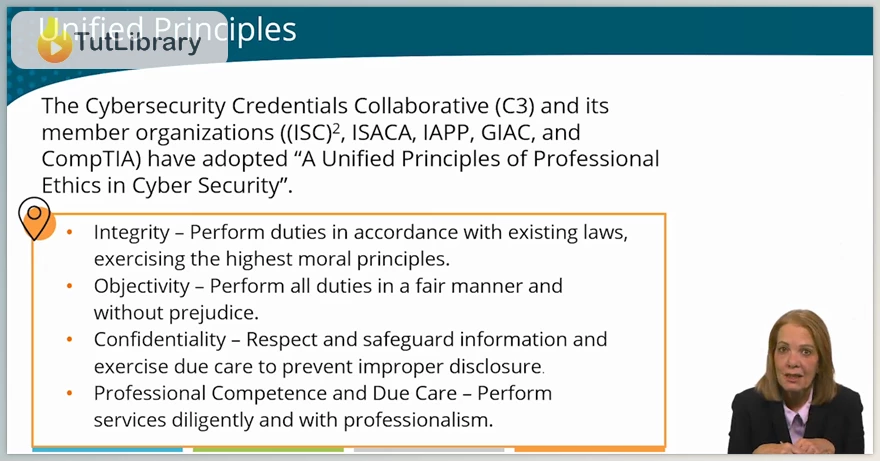
- 1.1 Organizational and Professional Ethics
- Lesson 2: Understand and Apply Security Concepts
- Learning objectives
- 2.1 Information and Cybersecurity Principles
- Lesson 3: Evaluate, Apply, and Sustain Security Governance Principles
- Learning objectives
- 3.1 Strategic Alignment
- 3.2 Organizational Roles and Responsibilities
- 3.3 Security Control Frameworks
- Lesson 4: Understand Legal, Regulatory, and Compliance Issues that Pertain to Information Security in a Holistic Context
- Learning objectives
- 4.1 Regulatory and Compliance Obligations
- 4.2 Intellectual Property Transborder Data Flow
- 4.3 Privacy Principles
- 4.4 Cybercrime and Data Breaches
- Lesson 5: Understand Requirements for Investigation Types
- Learning objectives
- 5.1 Investigation Objectives and Requirements
- Lessons 1 through 5: Deep Dive Quiz
- Lessons 1-5 Deep Dive Quiz
- Lesson 6: Develop, Document, and Implement Security Policy, Standards, Procedures, and Guidelines
- Learning objectives
- 6.1 Governance Documents
- Lesson 7: Identify, Analyze, Assess, Prioritize, and Implement Business Continuity (BC) Requirements
- Learning objectives
- 7.1 Business Continuity Planning
- 7.2 Business Impact Analysis
- Lesson 8: Contribute to and Enforce Personnel Security Policies and Procedures
- Learning objectives
- 8.1 Workforce Lifecycle Security
- 8.2 Workforce and Third-party Policies and Agreements
- Lesson 9: Understand and Apply Risk Management Concepts
- Learning objectives
- 9.1 Risk Basics
- 9.2 Risk Assessment
- 9.3 Risk Analysis
- 9.4 Risk Response and Treatment
- 9.5 Risk Mitigation Controls
- 9.6 Risk Monitoring, Reporting, and Maturity
- Lessons 6 through 9: Deep Dive Quiz
- Lesson 6 - 9 Deep Dive Quiz
- Lesson 10: Understand and Apply Threat Modeling Concepts and Methodologies
- Learning objectives
- 10.1 Threat Actors and Attributes
- 10.2 Attack Vectors - Digital Infrastructure
- 10.3 Attack Vectors - People
- 10.4 Attack Vectors - Code
- 10.5 Threat Modeling and Intelligence
- Lesson 11: Apply Supply Chain Risk Management (SCRM) Concepts
- Learning objectives
- 11.1 Supply Chain Relationships and Risks
- 11.2 Supply Chain Risk Management and Mitigation
- Lesson 12: Establish and Maintain a Security Awareness, Education, and Training Program
- Learning objectives
- 12.1 SETA Principles and Practices
- 12.2 Emerging SETA Trends, Techniques, and Topics
- Lessons 10 through 12: Deep Dive Quiz and Lab
- Lesson 10 - 12 Deep Dive Quiz
- Module 2: Domain 2 Asset Security
- Module Introduction
- Lesson 13: Identify and Classify Information and Assets
- Learning objectives
- 13.1 Asset Classification
- Lesson 14: Establish Information and Asset Handling Requirements
- Learning objectives
- 14.1 Asset Handling Requirements
- Lesson 15: Provision Information and Assets Securely
- Learning objectives
- 15.1 Asset Management
- Lesson 16: Manage Data Lifecycle
- Learning objectives
- 16.1 Data Management
- 16.2 Data Collection, Retention, and Archiving
- 16.3 Data Deletion and Media Destruction
- Lesson 17: Ensure Appropriate Asset Retention
- Learning objectives
- 17.1 Asset Retention and Retirement
- Lesson 18: Determine Data Security Controls and Compliance Requirements
- Learning objectives
- 18.1 Control Baselines
- 18.2 Data Protection Methods
- Lessons 13 through 18: Deep Dive Quiz
- Lessons 13 - 18 Deep Dive Quiz
- Module 3: Domain 3 Security Architecture and Engineering
- Module Introduction
- Lesson 19: Research, Implement, and Manage Engineering Processes using Secure Design Principles
- Learning objectives
- 19.1 Secure Design Principles
- 19.2 Zero Trust and Secure Access Service Edge (SASE)
- Lesson 20: Understand the Fundamental Concepts of Security Models
- Learning objectives
- 20.1 Information Security Models
- Lesson 21: Select Controls Based Upon Systems Security Requirements
- Learning objectives
- 21.1 Security Evaluation Criteria
- Lesson 22: Understand Security Capabilities of Information Systems
- Learning objectives
- 22.1 Trusted Computing Base
- Lessons 19 through 22: Deep Dive Quiz
- Lessons 19 - 22 Deep Dive Quiz
- Lesson 23: Assess and Mitigate the Vulnerabilities of Security Architectures, Designs, and Solution Elements
- Learning objectives
- 23.1 Client-based, Server-based, and Distributed Systems
- 23.2 Database Management Systems
- 23.3 Operational Technology (OT)
- 23.4 Cloud-based Systems
- 23.5 Internet of Things (IoT IIoT) Systems
- 23.6 Virtualization
- 23.7 Automation and Solution Elements
- Lesson 23: Deep Dive Quiz
- Lesson 23 Deep Dive Quiz
- Lesson 24: Select and Determine Cryptographic Solutions
- Learning objectives
- 24.1 Cryptography Primer
- 24.2 Encryption
- 24.3 Hashing and Digital Signatures
- 24.4 PKI and Digital Certificates
- 24.5 Emerging Cryptography
- Lesson 25: Understand Methods of Cryptanalytic Attacks
- Learning objectives
- 25.1 Cryptographic Attacks
- 25.2 Post-Exploitation Attacks
- 25.3 Ransomware
- Lesson 24 through 25: Deep Dive Quiz
- Lesson 24 - 25 Deep Dive Quiz
- Lesson 26: Apply Security Principles to Site and Facility Design
- Learning objectives
- 26.1 Physical Security Principles
- Lesson 27: Design Site and Facility Security Controls
- Learning objectives
- 27.1 Site and Building Controls
- 27.2 Environmental Impact
- Lesson 28: Manage the Information System Lifecycle
- Learning objectives
- 28.1 Information System Lifecycle
- Lessons 26 through 28: Deep Dive Quiz
- Lessons 26 - 28 Deep Dive Quiz
- Module 4: Domain 4 Communication and Network Security
- Module Introduction
- Lesson 29: Apply Secure Design Principles in Network Architecture
- Learning objectives
- 29.1 Network Models
- 29.2 Internet Protocol (IP)
- 29.3 Secure Protocols
- 29.4 Multilayer and Converged Protocols
- 29.5 Transport Architecture
- 29.6 Segmentation
- 29.7 Microsegmentation
- 29.8 Wireless Architecture
- 29.9 Wi-Fi Networks
- 29.10 Virtual Private Cloud
- 29.11 Continuous Monitoring
- Lesson 29: Deep Dive Quiz
- Lesson 29 Deep Dive Quiz
- Lesson 30: Secure Network Components
- Learning objectives
- 30.1 Transmission Media
- 30.2 Network Access Control
- 30.3 Endpoint Security
- Lesson 31: Implement Secure Communication Channels According to Design
- Learning objectives
- 31.1 Voice, Video, and Collaboration (CDN)
- 31.2 Secure Remote Access Communications
- Lessons 30 through 31: Deep Dive Quiz
- Lessons 30 - 31 Deep Dive Quiz
- Module 5: Domain 5 Identity and Access Management (IAM)
- Module Introduction
- Lesson 32: Control Physical and Logical Access to Assets
- Learning objectives
- 32.1 Access Control Fundamentals
- Lesson 33: Design Identification and Authentication Strategy
- Learning objectives
- 33.1 Identity Management (IdM)
- 33.2 Authentication and Credential Management
- 33.3 Biometric Authentication
- Lesson 34: Federated Identity with a Third-party Service
- Learning objectives
- 34.1 Federated Identity Management
- Lesson 35: Implement and Manage Authorization Mechanisms
- Learning objectives
- 35.1 Authorization and Access Controls
- Lesson 36: Manage the Identity and Access Provisioning Lifecycle
- Learning objectives
- 36.1 Identity and Access Management (IAM)
- Lesson 37: Implement Authentication Systems
- Learning objectives
- 37.1 Implementing Authentication Systems
- 37.2 Authentication and Access Control Attacks
- Lessons 32 through 37: Deep Dive Quiz
- Lessons 32 - 37 Deep Dive Quiz
- Module 6: Domain 6 Security Assessment and Testing
- Module Introduction
- Lesson 38: Design and Validate Assessment, Test, and Audit Strategies
- Learning objectives
- 38.1 Assessment and Audit Strategies
- 38.2 Planning Engagements
- Lesson 39: Conduct Security Controls Testing
- Learning objectives
- 39.1 Vulnerability Testing and Assessment
- 39.2 Penetration Testing and Attack Simulations
- 39.3 Code and Interface Testing
- Lessons 38 through 39: Deep Dive Quiz
- Lessons 38 - 39 Deep Dive Quiz
Who is this course for?
- Some knowledge in cybersecurity and experience can be in some areas of the CISSP
- Success junkies or people who seek success in their CISSP exam.
Click on the links below to Download CISSP, 4th Edition - Sari Greene!
You are replying to :















