
“Ethical Hacking: Design an Info Stealer using Python 3” will allow you to create a potent “Info Stealer” tool. Use this tool for educational purposes to understand cyber security or as a practical tool for exercises in Red Team. You don’t need to have programmed before; each line of code is analyzed and dissected.
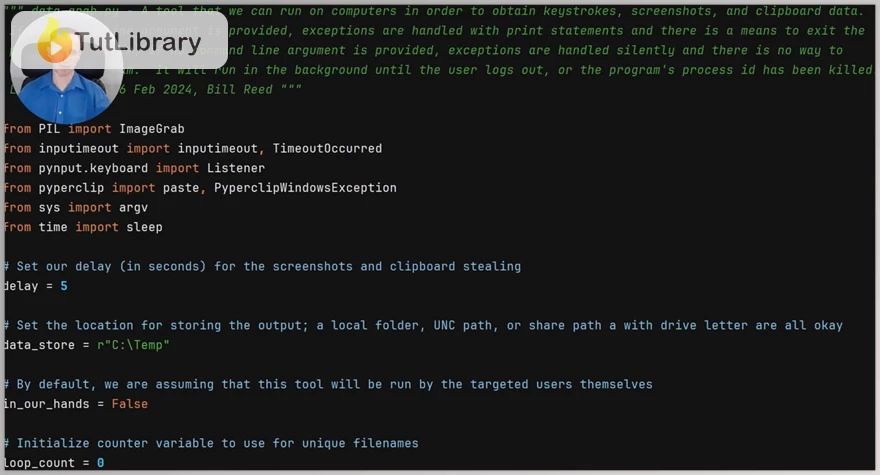
"Ethical Hacking: Design an Info Stealer using Python 3" will take you through developing an Info Stealer that can perform keylogging, record screenshots, and monitor clipboard activity. It could be written to store data on network shares or locally, according to your needs. As beginners, we shall find our feet within the intricacies of Python while intermediate coders discern advanced approaches, all culminating in producing a sophisticated set of tools.
Python Code Compilation into A Standalone Executable at Final Stages Ensuring That Target Systems Are Not Dependent On The Presence Of Python As Well As Windows Commands Mostly Used In Corporate Or Governmental Networks Which Are Running Microsoft Active Directory And Ethical Use Of These Commands Aid With Right Credentials Results To Remote Execution Inside Domain’s Ecology And This Expands Your Cybersecurity Techniques Capability.
The last stages guide you on converting your Python code into stand-alone executables that do not rely on Python being present on target systems. Also, ensure that one has insider knowledge about windows commands used mostly in corporate or governmental networks running Microsoft active directory. By ethically leveraging these command lines with proper credentials, one can remotely execute anything within the domain environment, increasing their strength in cyberspace.
Ethical Hacking: Design an Info Stealer using Python 3 Table of Contents:
- Introduction and Installations (02:54)
- Installing Python 3.x on Windows OS (02:44)
- Installing PyCharm Community Edition (03:02)
- Creating the Project and Beginning Coding with an Argument Check (15:48)
- Python Specifics from Lecture 4 (5 questions)
- Implementation of the Keylogger Functionality (19:19)
- Python Specifics from Lecture 5 (5 questions)
- Implementation of Code That Copies Out the Clipboard's Contents (10:07)
- Python Specifics from Lecture 6 (3 questions)
- Implementation of Code That Takes Screenshots and Allows for a Clean Exit (14:41)
- Python Specifics from Lecture 7 (5 questions)
- Creating a One-File Executable Build (Part 1) (17:08)
- Creating a One-File Executable Build (Part 2), and Defeating Microsoft Defender (11:26)
- Configuration of, and Running the Ethical Hacking Tool on Linux (07:19)
- Python Specifics from Lectures 8-10 (7 questions)
- Conclusion (00:34)
- Bonus Lesson (03:40)
Who is this course for?
- The program is suitable for python enthusiasts who wish to acquire knowledge on ethical hacking tool development It is a practical course that provides beginners with an entry point into the world of ethical hacking.
- This is the best place to start for budding white-hat hackers looking to get their hands dirty.
Click on the links below to Download Ethical Hacking: Design an Info Stealer using Python 3!
You are replying to :















