
From the name ‘Hacking Mobile Devices,’ this is a beginner’s course that gives an insight into some important techniques without advanced knowledge or skills. Topics include social engineering, malware obfuscation, network exploitation, and ethical hacking covering, which will enable the participants to appreciate mobile device security. It includes the networking and port scanning methods and style, the use of exploits for information retrieval, and the use of BeeF XSS in collecting data from iOS and Android. As a result of stressing ethical conduct, the course highlights issues of using information technology resources responsibly with an ethical perspective on cybersecurity.
Responsive to Red Teamers and Mobile Penetration Testers, this course, “Hacking Mobile Devices,” completely promotes ethical hacking only. Offensive security mechanisms will be applied and utilized in this environment with full legal awareness and agreed ethical standards of the participants enrolled in the training. Thus, emphasizing the learning process and personal professional growth, the proposed “Hacking Mobile Devices” is designed to raise contributions of such personnel to the field of cybersecurity, improve their knowledge about the threats of mobile devices, and strengthen the security of cyber infrastructures.
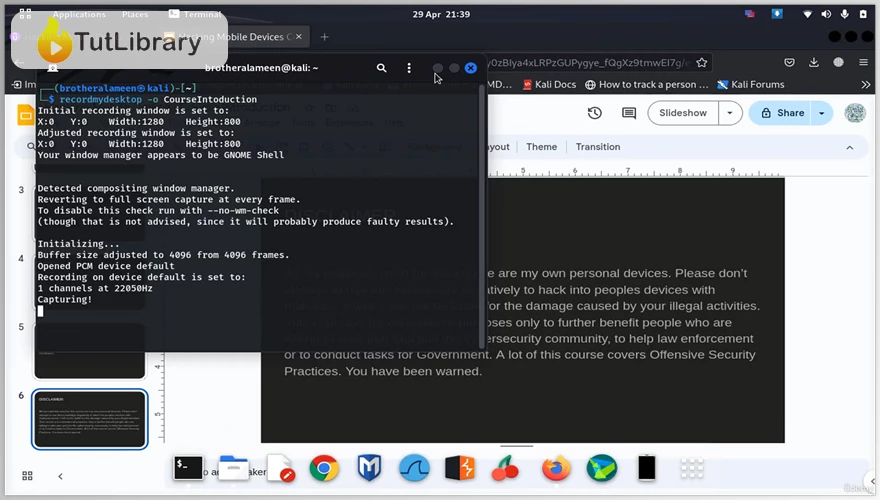
Hacking Mobile Devices Table of Contents:
- Self Introduction (00:40)
- Understanding Terminologies (01:11)
- Introducing the Course (02:12)
- Scan for Android Devices over the Network (05:51)
- Scan for Open Ports on an Android Device (10:47)
- Exploit a Vulnerability (10:44)
- Setting up and Using an IP Logger (22:30)
- Setting up and Using Seeker (22:11)
- Setting up and Using a Canary Token (21:40)
- Setting up and Using Camera Phisher (14:21)
- Social Engineering Techniques (20:17)
- Using BeeFXSS (Internally) (36:40)
- Setting up BeeF XSS for Internet Usage (14:43)
- Setup a msfvenom Payload (19:30)
- Undetectable Payloads (01:15)
- Apply Obfuscation Using Encoders (09:16)
- Exploit the Android Device (20:15)
- Creating a Trojan (Manual Method) (01:01)
- Conclusion (00:49)
Who is this course for?
- Beginners
Click on the links below to Download Hacking Mobile Devices!
You are replying to :















