
The book “Learning Kali Linux - Ric Messier” guides you to utilize the strengths of Kali Linux, your best companion for security checking and much more, possessing over 600 utilities. In this book written by Ric Messier from Mandiant, you will be able to learn updates on the chapter and the basic knowledge of reverse engineering, forensic analysis, and malware investigation. Informational search is also useful in that helpful review questions assist in confirming comprehension along the way.
So, let’s dive into these steps, where you will learn about security testing from basic installation of Kali Linux on various systems to commands on various tools of Kali Linux. This guide is easy to follow, from the fundamentals of penetration testing to how to write elaborate, detailed reports with examples. If you are a beginner or if you are a long-time worker in cybersecurity, this book, titled “Learning Kali Linux - Ric Messier,” distils the discussion to understandable microchunks that will explain it to you.
In the end, you will be able to use Kali Linux with great ease. You can design individual steps of security tests and even perform complex attack scenarios.
Learning Kali Linux - Ric Messier Table of Contents:
- Foundations of Kali Linux
- Heritage of Linux
- Acquiring and Installing Kali Linux
- Virtual Machines
- Windows Subsystem for Linux (WSL)
- Desktops: Xfce, GNOME, Cinnamon, and MATE
- Using the Command Line
- File and Directory Management
- Process and Service Management
- Package Management
- Remote Access
- Log Management
- Network Security Testing Basics
- Security Testing Overview
- Network Security Testing and Monitoring
- Stress Testing and Denial-of-Service Tools
- Encryption Testing and Packet Captures
- Poisoning Attacks: ARP Spoofing and DNS Spoofing
- Reconnaissance
- Open Source Intelligence and Google Hacking
- Automating Information Gathering: Recon-NG and Maltego
- DNS Reconnaissance and Passive Reconnaissance
- Port Scanning with Nmap
- Service Scanning and Manual Interaction
- Looking for Vulnerabilities
- Understanding Vulnerabilities and Vulnerability Types
- Vulnerability Scanning: Local and Remote
- Network Device and Database Vulnerabilities
- Identifying New Vulnerabilities and Root Kits
- Automated Exploits
- Introduction to Exploits and Exploit Database
- Working with Metasploit: Modules and Exploitation
- Social Engineering and Cisco Attacks
- Owning Metasploit
- Scanning for Targets: Port and SMB Scanning
- Exploiting Your Target with Meterpreter
- Privilege Escalation and Pivoting to Other Networks
- Wireless Security Testing
- Overview of Wireless Technologies: 802.11, Bluetooth, Zigbee
- WiFi Attacks and Testing Tools
- Injection Attacks and Password Cracking on WiFi
- Bluetooth Testing and Home Automation Testing
- Web Application Testing
- Web Architecture Overview
- Web-Based Attacks: SQL Injection, XSS, CSRF, Session Hijacking
- Using Proxies: Burp Suite, ZAP, WebScarab, Paros Proxy
- Automated Web Attacks and CMS Testing
- Cracking Passwords
- Password Storage and Acquiring Passwords
- Offline and Online Password Cracking
- Web-Based Cracking Techniques
- Advanced Techniques and Concepts
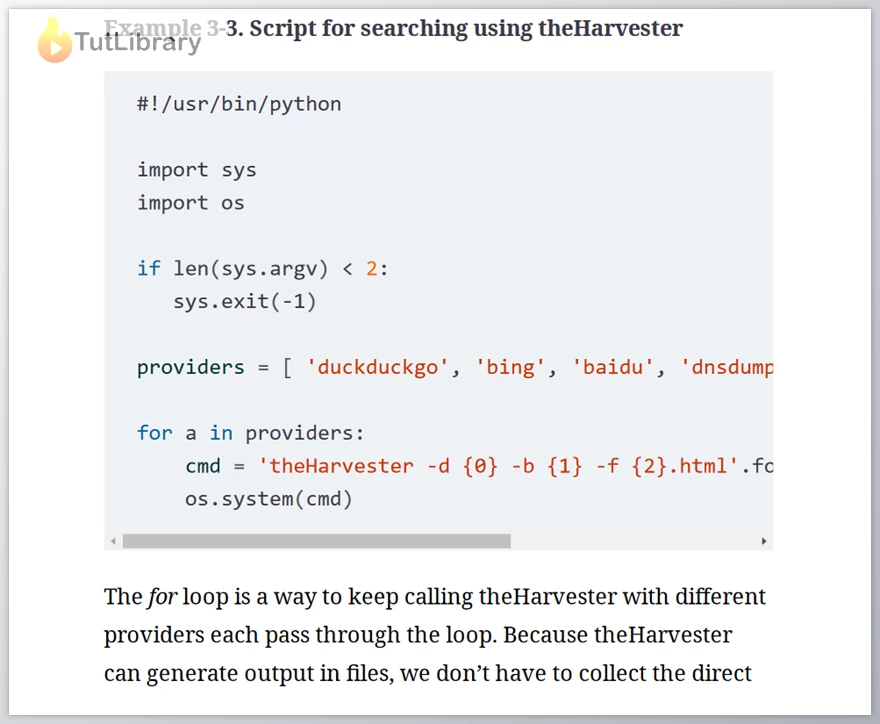
- Programming Basics and Writing Nmap Modules
- Buffer Overflows and Heap Overflows
- Extending Metasploit and Maintaining Access.
Who is this course for?
- Penetration testers
- Security professionals
- Individuals interested in cybersecurity
- For Kali Linux and security testing enthusiasts, especially for the newbies.
Click on the links below to Download Learning Kali Linux - Ric Messier!
You are replying to :
















